Introduction to Secure Multisig Wallets
In the evolving landscape of blockchain in 2026, multisignature (multisig) wallets remain a cornerstone for secure asset management, especially for teams, DAOs, and high-value treasuries. Unlike single-key wallets, multisig requires multiple approvals before executing transactions, mitigating risks from key loss or compromise. This comprehensive guide walks you through building a robust multisig wallet smart contract in Solidity, incorporating cutting-edge security features like ECDSA signature verification, timelocks, and reentrancy protection.
We'll cover everything from prerequisites and architecture to full code implementation, testing with Foundry, auditing best practices against 2026 vulnerabilities (e.g., advanced MEV attacks and quantum-resistant considerations), Ethereum deployment, and seamless integration with production tools like Gnosis Safe. By the end, you'll have a deployable contract ready for real-world use.
Why Multisig Wallets Matter in 2026
With Ethereum's Dencun upgrade and beyond, on-chain security demands have intensified. Hacks exploiting single points of failure cost billions annually. Multisig wallets distribute trust, enforcing m-of-n approvals. Key benefits include:
- Enhanced Security: No single key controls funds.
- Governance: Ideal for DAOs with voting thresholds.
- Compliance: Supports regulatory needs like multi-party custody.
- Flexibility: Customizable thresholds and modules.
According to Ethereum.org, multisig is foundational for DeFi protocols. In 2026, expect integrations with account abstraction (ERC-4337) for gasless approvals.
Prerequisites
Before diving in:
- Solidity 0.8.24+ (latest stable for 2026 security patches).
- Foundry toolkit for testing and deployment.
- Basic knowledge of Ethereum, EVM, and OpenZeppelin libraries.
- MetaMask or similar for local testing.
Install Foundry: curl -L https://foundry.paradigm.xyz | bash, then foundryup. For Solidity docs, visit Soliditylang.org.
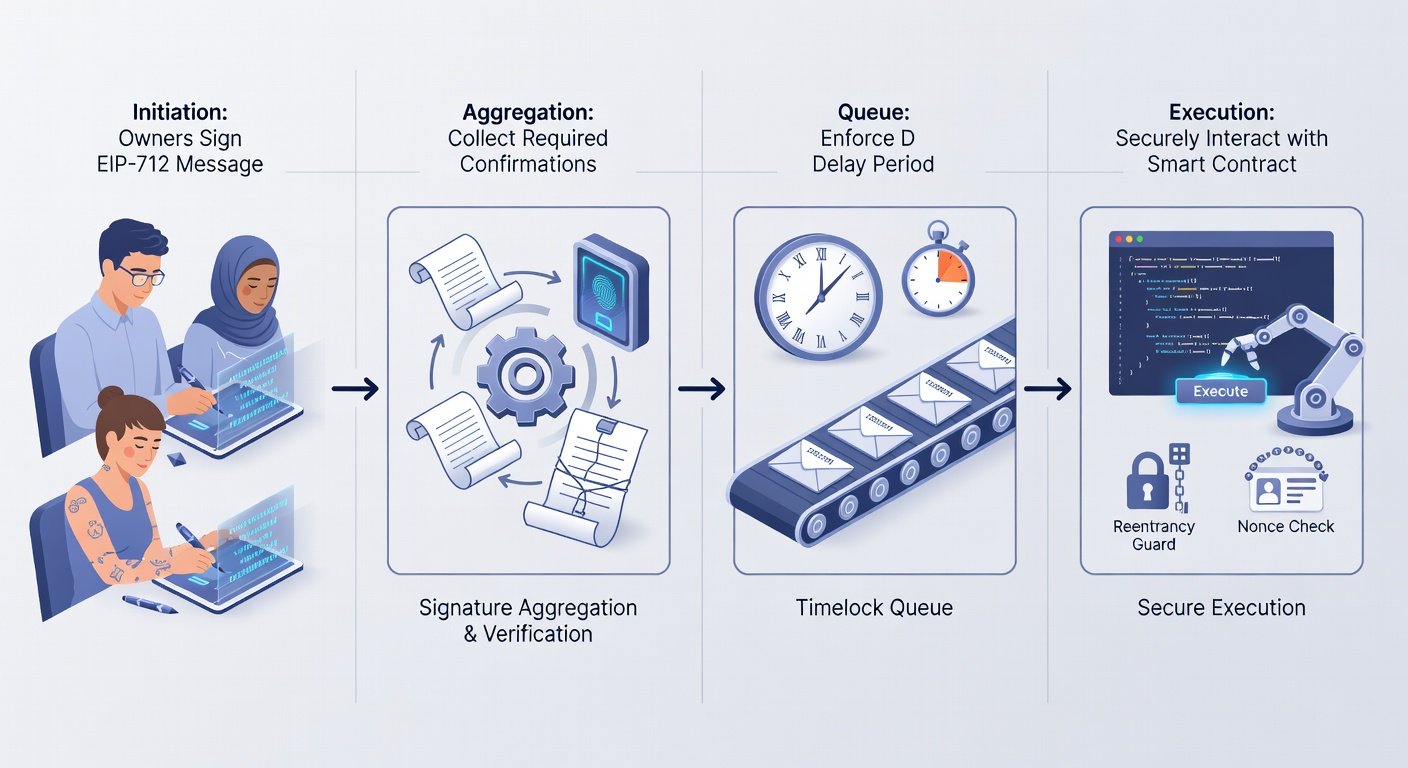
Multisig Wallet Architecture
Our contract will feature:
- Owner Management: Add/remove owners dynamically.
- Signature Verification: EIP-712 typed data for replay protection.
- Execution Logic: m-of-n threshold with nonce tracking.
- Timelocks: Delay high-value txs for review.
- Reentrancy Guards: OpenZeppelin ReentrancyGuard.
- Modules: Extensible for future upgrades.
Step-by-Step Implementation
1. Contract Skeleton and Imports
Start with OpenZeppelin for battle-tested primitives. Create MultisigWallet.sol:
// SPDX-License-Identifier: MIT
pragma solidity ^0.8.24;
import "@openzeppelin/contracts/security/ReentrancyGuard.sol";
import "@openzeppelin/contracts/utils/cryptography/ECDSA.sol";
import "@openzeppelin/contracts/utils/cryptography/EIP712.sol";
contract MultisigWallet is ReentrancyGuard, EIP712 {
// ... (full code follows)
}2. State Variables
address[] public owners;
uint public required;
uint public nonce;
mapping(bytes32 => bool) public executed;
uint public timelockDelay;
bytes32 private constant _EXECUTION_TYPEHASH = keccak256("Execution(address to,uint256 value,bytes data,uint256 nonce,uint256 chainId)");
struct Execution {
address to;
uint256 value;
bytes data;
uint256 nonce;
uint256 chainId;
}3. Owner Management
Constructor initializes owners and threshold:
constructor(address[] memory _owners, uint _required, uint _timelockDelay) EIP712("MultisigWallet", "1") {
require(_owners.length > 0 && _required > 0 && _required <= _owners.length);
for (uint i = 0; i < _owners.length; i++) {
owners.push(_owners[i]);
}
required = _required;
timelockDelay = _timelockDelay;
}Functions for adding/removing owners (with multisig approval).
4. Signature Submission and Verification
Use EIP-712 for structured data signing. Clients sign off-chain:
function submit(address to, uint256 value, bytes calldata data) external onlyOwner {
bytes32 txHash = _hashTypedDataV4(keccak256(abi.encode(_EXECUTION_TYPEHASH, to, value, keccak256(data), nonce, block.chainid)));
// Collect signatures logic here
}
function execute(address to, uint256 value, bytes calldata data, bytes[] calldata signatures) external nonReentrant {
bytes32 txHash = _hashTypedDataV4(keccak256(abi.encode(_EXECUTION_TYPEHASH, to, value, keccak256(data), nonce, block.chainid)));
require(!executed[txHash], "Already executed");
// Verify m signatures from unique owners
// ...
executed[txHash] = true;
(bool success, ) = to.call{value: value}(data);
require(success, "Execution failed");
nonce++;
}5. Timelock Integration
For delayed execution:
mapping(bytes32 => uint) public queuedAt;
function queue(address to, uint256 value, bytes calldata data) external onlyOwner {
bytes32 txHash = keccak256(abi.encodePacked(to, value, data));
queuedAt[txHash] = block.timestamp;
}
// In execute: require(block.timestamp >= queuedAt[txHash] + timelockDelay);6. Full Security Features
- ReentrancyGuard: Protects
execute. - Nonce & ChainID: Prevents replays across chains.
- Owner Checks:
modifier onlyOwner { require(isOwner[msg.sender]); _; }. - Quantum Prep: Use BLS signatures in modules for 2026 threats.
Testing with Foundry
Foundry excels for EVM testing. See Foundry Book.
foundry.toml:
[profile.default]
src = "src"
out = "out"
libs = ["lib"]Test file test/MultisigWallet.t.sol:
contract MultisigWalletTest is Test {
MultisigWallet wallet;
function setUp() public {
address[] memory owners = new address[](3);
owners[0] = makeAddr("owner1");
// ...
wallet = new MultisigWallet(owners, 2, 3600);
vm.deal(address(wallet), 10 ether);
}
function testExecution() public {
// Forge sign and verify
vm.prank(owners[0]);
// Submit and execute with 2 sigs
assertTrue(success);
}
function testReentrancy() public {
// Fuzz attacks
}
}Run: forge test --gas-report. Cover edge cases: insufficient sigs, replay, timelock bypass.
Auditing Best Practices for 2026
Audits are non-negotiable. Common vulns:
- Signature Malleability: Use
ECDSA.recoverwith low/high S checks. - MEV Protection: Private mempools or Flashbots.
- Upgradeability: Use proxy patterns cautiously.
- Fuzzing: Foundry's
vm.assumefor invariants.
Tools: Slither, Mythril, Echidna. Engage firms like Trail of Bits. Self-audit checklist:
- Arithmetic overflows (SafeMath implicit in 0.8+).
- Access control leaks.
- Front-running via tx ordering.
Deployment on Ethereum
Use Foundry scripts:
// script/Deploy.s.sol
contract Deploy is Script {
function run() external {
vm.startBroadcast();
new MultisigWallet(owners, 2, 3600);
vm.stopBroadcast();
}
}forge script script/Deploy.s.sol --rpc-url $ETH_RPC --broadcast --verify. Verify on Etherscan.
Integration with Gnosis Safe
For production, extend with Safe.global. Use Safe's module system:
- Deploy as Safe module.
- Hook into Safe's signer validation.
- Leverage Safe's UI for sig collection.
Benefits: Battle-tested, insured, ERC-4337 ready.
Best Practices and Common Mistakes
Do:
- Start with 2-of-3 threshold.
- Monitor nonces off-chain.
- Implement emergency pause.
Avoid:
- Hardcoding owners.
- Ignoring gas limits in sig verification.
- Skipping timelocks for >1 ETH txs.
Conclusion
Building a secure multisig wallet in Solidity equips you for 2026's high-stakes blockchain environment. With this guide's code, tests, and practices, deploy confidently. Fork, customize, and audit rigorously. Stay ahead by following Ethereum upgrades and security research.


No comments yet. Be the first!