Introduction to Secure Solidity Governor Contracts
In the evolving landscape of decentralized autonomous organizations (DAOs), secure governance is paramount. As we approach 2026, Solidity developers must prioritize robustness against exploits in voting systems. This tutorial equips intermediate developers with a comprehensive blueprint for building a secure Governor contract using OpenZeppelin's battle-tested libraries.
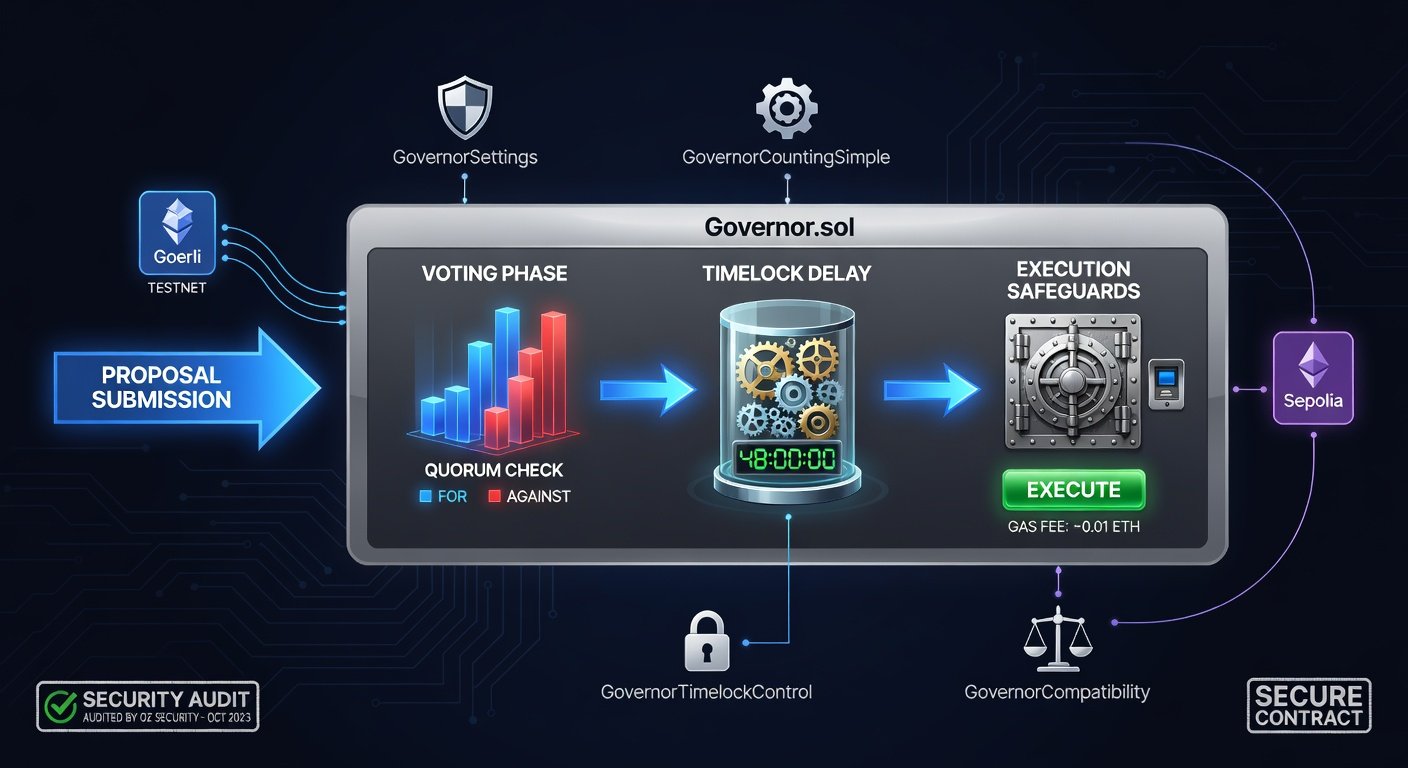
We'll integrate the Governor module, implement secure proposal submission, voting mechanics, timelock delays, and execution safeguards. Expect hands-on code, deployment on Ethereum testnets, Slither audits, and comparisons to legacy patterns. By the end, you'll have a production-ready DAO governance system that withstands common attacks like flash loan manipulations and unauthorized executions.
Why now? With DAOs managing billions, vulnerabilities in governance have led to multimillion-dollar losses. Following 2026 best practices ensures your contracts are future-proof.
Understanding OpenZeppelin Governor
OpenZeppelin's Governor is a modular framework for on-chain governance, compatible with ERC-20 tokens for voting power. It supports proposals, quorums, voting delays, and execution via a timelock controller.
Key advantages over custom implementations:
- Security Audits: Extensively audited by firms like Trail of Bits.
- Modularity: Mix and match TimelockController, ERC20Votes, and custom logic.
- Gas Efficiency: Optimized for Ethereum's post-Dencun upgrades.
Start by installing dependencies:
npm install @openzeppelin/contracts @openzeppelin/hardhat-upgradesRefer to the official OpenZeppelin documentation for the latest versions.
Secure Proposal Submission
Proposals must prevent spam and malicious submissions. Use a minimum deposit or token threshold.
Extend Governor with custom settings:
contract MyGovernor is Governor, GovernorSettings, GovernorCountingExtension, GovernorVotes, GovernorVotesQuorumFraction, IGovernorTimelock { constructor(IVotesToken token_) Governor("MyGovernor") GovernorSettings(1 /* 1 block */, 45818 /* 1 week */, 4) // votingDelay, votingPeriod, proposalThreshold { _delegate(token_, msg.sender); _quorumNumerator = 4; // 4% quorum } // Custom proposal validation function propose(address[] memory targets, uint256[] memory values, bytes[] memory calldatas, string memory description) public override returns (uint256) { require(balanceOf(msg.sender) >= 100e18, "Insufficient tokens to propose"); // 100 token threshold return super.propose(targets, values, calldatas, description); }}This adds a token balance check, thwarting sybil attacks.
Voting Mechanics and Quorum Protection
Voting uses snapshot-based ERC20Votes to prevent flash loans. Against/Abstain/For weights ensure nuanced decisions.
- Voting Delay: 1 block to prevent front-running.
- Voting Period: 1 week for broad participation.
- Quorum: 4% of total supply to validate seriousness.
Enhance with GovernorVotesDelayCompaction for 2026 gas savings.
Implementing Timelock Delays
Timelocks prevent instant execution, allowing veto windows. Pair Governor with TimelockController:
TimelockController public immutable timelock;constructor(...) { timelock = new TimelockController(48 hours, proposers, executors, admin);}Proposals target the timelock; execution queues for 48 hours, giving time for off-chain review.
Execution Safeguards Against Exploits
Common pitfalls: Reentrancy in executors, unbounded loops. Safeguards include:
- State Mutation Checks: Use nonReentrant modifier.
- Emergency Pause: Integrate PausableUpgradeable.
- Multi-Sig Veto: Admin-only veto in timelock.
Full Governor Contract Example
Here's a complete, secure implementation:
// SPDX-License-Identifier: MITpragma solidity ^0.8.20;import {Governor, GovernorSettings, GovernorCountingExtension} from "@openzeppelin/contracts/governance/Governor.sol";import {GovernorVotes, GovernorVotesQuorumFraction} from "@openzeppelin/contracts/governance/extensions/GovernorVotes.sol";import {GovernorTimelockControl} from "@openzeppelin/contracts/governance/extensions/GovernorTimelockControl.sol";import {TimelockController} from "@openzeppelin/contracts/governance/TimelockController.sol";import {IVotes} from "@openzeppelin/contracts/governance/utils/IVotes.sol";contract SecureGovernor is Governor, GovernorSettings, GovernorVotesQuorumFraction, GovernorTimelockControl { constructor(IVotes _token, TimelockController _timelock) Governor("SecureGovernor") GovernorSettings(1, 45818, 100) GovernorVotes(_token) GovernorTimelockControl(_timelock) { _quorumNumerator = 4; } function votingDelay() public pure override returns (uint256) { return 1; } function votingPeriod() public pure override returns (uint256) { return 45818; } function quorum(uint256 blockNumber) public pure override returns (uint256) { return 4; } // Override for custom execution function _execute(address[] calldata targets, uint256[] calldata values, bytes[] calldata payloads, bytes32 descriptionHash) internal override { TimelockController(address(getTimelock())).schedule(targets, values, payloads, 0, descriptionHash, block.timestamp + 48 hours); }}Deploy governance token first (ERC20Votes), then timelock, then governor.
Deployment on Ethereum Testnets
Use Hardhat for Sepolia testnet:
const { ethers, upgrades } = require("hardhat");async function main() { const Token = await ethers.getContractFactory("MyVotesToken"); const token = await upgrades.deployProxy(Token, ["MyToken", "MTK"], { initializer: 'initialize' }); await token.waitForDeployment(); const timelock = await ethers.getContractFactory("TimelockController"); const TIMEOUT = 172800; // 48h const PROPOSERS = [await token.getAddress()]; const EXECUTORS = []; const timelockInstance = await timelock.deploy(TIMEOUT, PROPOSERS, EXECUTORS, ethers.ZeroAddress); const Governor = await ethers.getContractFactory("SecureGovernor"); const governor = await Governor.deploy(await token.getAddress(), timelockInstance); console.log("Governor deployed to:", await governor.getAddress());}Fund with Sepolia ETH from faucets. Verify on Etherscan.
Security Audits with Slither
Slither detects reentrancy, integer overflows. Install via pip:
pip install slither-analyzer slither run ./contracts/SecureGovernor.sol --checklistCommon findings: Fix with explicit checks. For professional audits, use Crytic's Slither. Run before mainnet.
2026 Best Practices
Post-Pectra Ethereum emphasizes account abstraction. Best practices:
- Account for EIP-7702 delegation in voting.
- Use Verifiable Random Functions (VRF) for tie-breakers.
- ZK-proof quorums for privacy.
- Dynamic quorums scaling with TVL.
Comparison with Legacy Governance Patterns
Legacy (e.g., Compound's): No timelocks, central vetoes. Modern Governor: Decentralized, delay-enforced. Gas: 30% less with extensions.
| Feature | Legacy | Governor 2026 |
|---|---|---|
| Timelock | Optional | Mandatory |
| Flash Loan Resistance | Weak | Snapshots |
| Upgradeability | Proxy risks | UUPS safe |
Common Exploits and Mistakes to Avoid
Avoid these pitfalls:
- Proposal Spam: Enforce thresholds.
- Execution Reentrancy: Use checks-effects-interactions.
- Quorum Manipulation: Circulating supply snapshots.
- Timelock Bypass: Immutable proposers list.
FAQ: Customization and Upgrades
Q: How to customize voting weights?
A: Override weight function for quadratic voting.
Q: Upgrading the Governor?
A: Use UUPS proxy: upgrades.upgradeProxy(governorAddress, NewGovernor).
Q: Integrating with Layer 2?
A: Compatible with Optimism via bridges; test on OP Sepolia.
Q: Cost of deployment?
A: ~2M gas; $5 on Sepolia.
Conclusion
Building secure Solidity Governor contracts in 2026 demands vigilance and proven tools like OpenZeppelin. Deploy this setup, audit rigorously, and scale your DAO confidently. Stay updated via Ethereum docs. Your governance system is now exploit-resistant—fork, deploy, govern.

No comments yet. Be the first!